Summary
Sprocket Security offers pentesting services and a free attack surface management (ASM) tool that helps companies find hidden assets: vulnerable subdomains, leaked credentials, dangling DNS records, and other exposures sysadmins often cannot see.
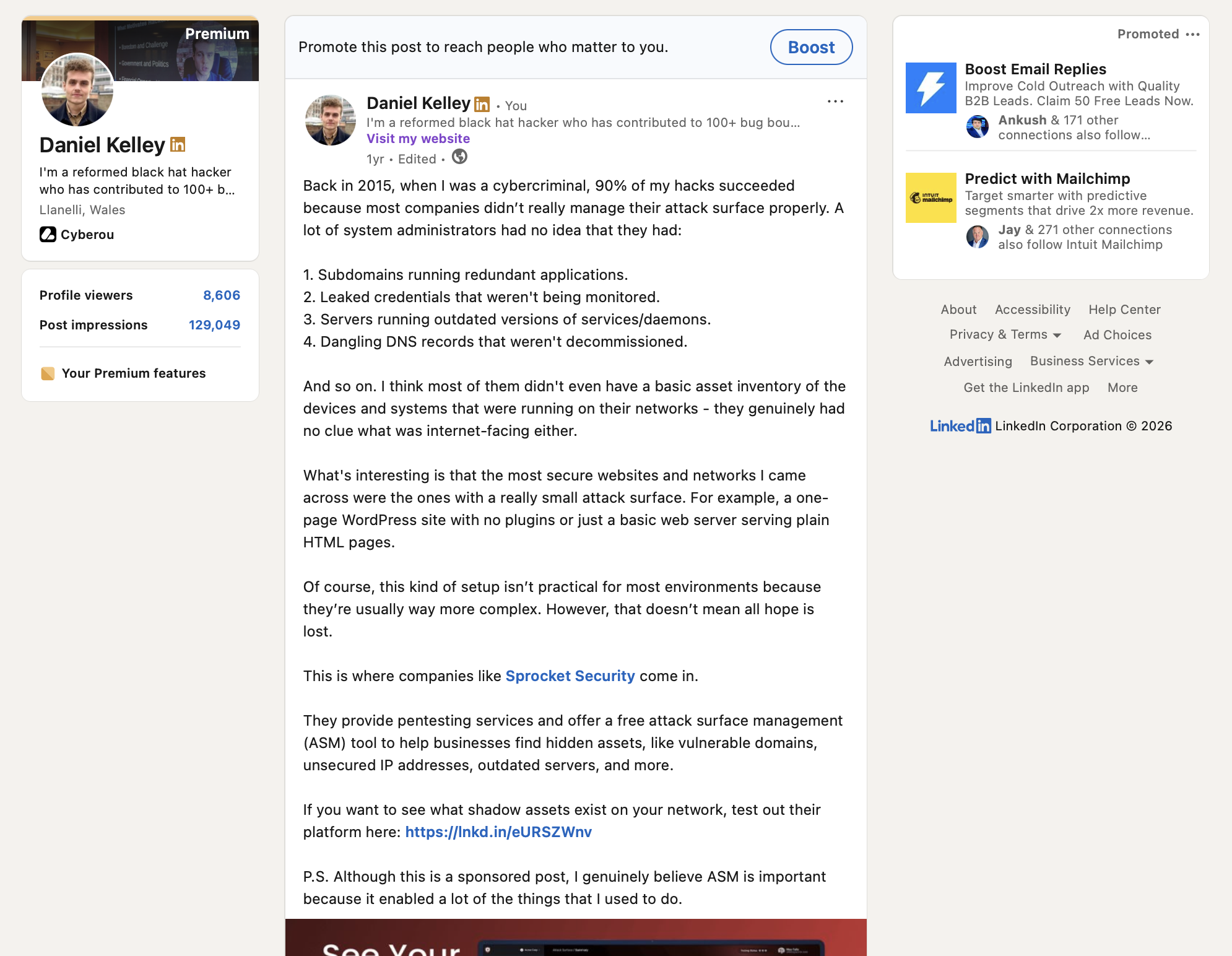
We wrote a sponsored LinkedIn post that opened with a first-person cybercriminal perspective on why unmanaged attack surface is an attacker's easiest route in, listed the specific failure modes from a 2015 attacker's-eye view, and wrapped back to Sprocket's free ASM tool as the practical defensive answer. 23K views and 178 likes from security practitioners on the free-tool CTA.
Challenge
Attack surface management is a crowded category competing with vulnerability management, EASM, and "modern pentesting" for practitioner attention. Sponsored posts that open with "discover your attack surface today" get scrolled past by the exact audience Sprocket needed to reach. The sponsored creative had to land as a practitioner take, not a product pitch.
The harder constraint was credibility. The "here are failures I saw" angle only works if the writer can actually describe the failures accurately. Generic lists of "common misconfigurations" read as vendor content immediately; specific, dated observations from a real attacker perspective read differently.
And the CTA had to convert. ASM tools compete on free-trial friction: the moment a vendor asks for a demo call or extensive form, the audience filters out. Sprocket's free ASM tool already had that solved; the sponsored creative just had to route readers to it cleanly.
Approach
We opened with a first-person cybercriminal perspective: back in 2015, 90% of hacks succeeded because most companies did not manage their attack surface properly. That opening puts the reader in a specific mindset (offensive voice, concrete memory) before the post goes anywhere near the vendor.
The middle of the post listed the exact failure modes that made those hacks easy:
- Subdomains running redundant applications
- Leaked credentials that were not being monitored
- Servers running outdated versions of services and daemons
- Dangling DNS records that had not been decommissioned
Specific, dated, checkable observations. Not a generic "common misconfigurations" list.
Sprocket Security landed as the answer: pentesting services and a free ASM tool that surfaces exactly those kinds of hidden assets. The CTA was the free-tool URL. A closing P.S. note acknowledged the sponsored disclosure but reinforced that ASM is genuinely important, because it enabled a lot of the things the writer used to do.
Results
The post cleared 23K views and 178 likes on LinkedIn. For a free-tool sponsored post in the crowded ASM/EASM category, the view-to-like ratio is the signal that matters: practitioners read the post, agreed the problem was worth investigating, and engaged publicly on a piece that clearly routed them to the free tool.
The comment section stayed on the technical content. Attack-surface failure modes and the 2015 anecdote drove discussion, not whether the post felt like an ad. The ex-cybercriminal opening paid off specifically because it sounded like a peer talking about their own experience.
For Sprocket Security, the execution gave growth a reusable template for sponsored creative in ASM: first-person practitioner opener, specific failure-mode list, product as answer, free-tool CTA, genuine closing note.